If you are upgrading, you do not need to upgrade your Apache installation. However, if you have upgraded your version of Tomcat, you will need to verify that the paths in your extraview.conf and httpd.conf files match the current paths to Tomcat - see the section "Configure Apache" below for instructions.
If you are upgrading, ExtraView now supports compressed javascript files. There is a configuration change needed to your Apache setup in order to take advantage of this - please see the section entitled Configuring Apache to Use JavaScript Compression at the bottom of this page.
The following steps will install Apache into the directory $BASE/httpd-2.2.21.
cd $INSTALL
gunzip httpd-2.2.21.tar.gz
tar xvf httpd-2.2.21.tar
cd httpd-2.2.21
./configure --prefix=$BASE/httpd-2.2.21 --enable-mods-shared=most --enable-ssl=shared
make
make install
The Apache web server is now installed in the directory $BASE/httpd-2.2.21. You can su to root and start/stop the apache server using the following commands:
$BASE/httpd-2.2.21/bin/apachectl start
$BASE/httpd-2.2.21/bin/apachectl stop
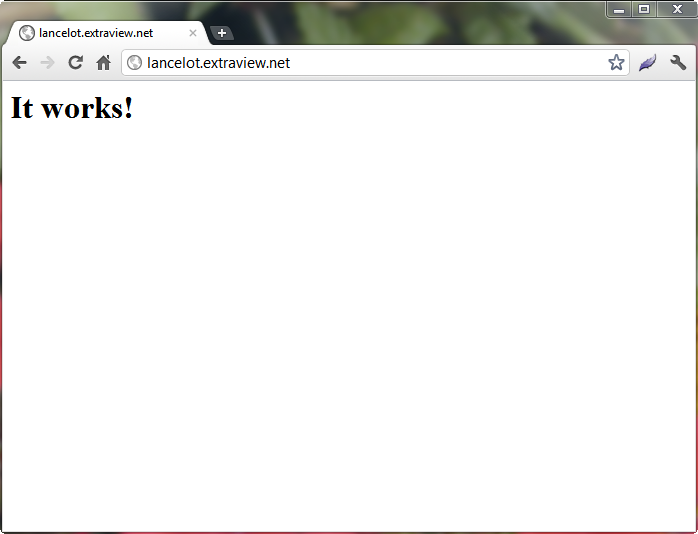
If you enter the URL of the server into a browser, for example http://server.domain.com, you should get the Apache test page.
cd $INSTALL
gunzip tomcat-connectors-1.2.32-src.tar.gz
tar xvf tomcat-connectors-1.2.32-src.tar
cd tomcat-connectors-1.2.32-src
cd native
./configure --with-apxs=$BASE/httpd-2.2.21/bin/apxs
make
make install
mod_jk.so will be installed in $BASE/httpd-2.2.21/modules
cd $INSTALL
gunzip tomcat-connectors-1.2.32-src.tar.gz
tar xvf tomcat-connectors-1.2.32-src.tar
cd tomcat-connectors-1.2.32-src
cd native
./configure --enable-netscape
cd netscape
make -f Makefile.solaris
copy the mod_jk.so file to $BASE/httpd-2.2.21/modules
cd $INSTALL
cp workers.properties $BASE/httpd_2.2.21/conf
Edit the Apache configuration file httpd.conf
vi $BASE/httpd-2.2.21/conf/httpd.conf
old line --> #ServerName new.host.name:80
new line --> ServerName extraview.yourcompany.com
Remember to use the URL of your server
old line --> ServerAdmin you@your.address
new line --> ServerAdmin serveradmin@yourcompany.com
Remember to use the email address of your administrator.
At the end of the file add the following line:
Include conf/extraview.conf
Save and exit httpd.conf
Copy the extraview.conf file:
cp $INSTALL/extraview.conf $BASE/httpd-2.2.21/conf
Edit the extraview.conf file and set the correct paths:
ServerName extraview.yourcompany.com
ServerAdmin serveradmin@yourcompany.com
DocumentRoot /usr/local/extraview/apache-tomcat-7.0.22/webapps/evj/
<Directory /usr/local/extraview/apache-tomcat-7.0.22/webapps/evj>
Options Indexes FollowSymLinks
</Directory>
Alias /evj/ "/usr/local/extraview/apache-tomcat-7.0.22/webapps/evj/"
JkWorkersFile /usr/local/extraview/httpd-2.2.21/conf/workers.properties
Locate the line at the bottom of the extraview.conf file that refers to mod_jk.so and make any needed changes to match your mod_jk file
that you either compiled or downloaded:
LoadModule jk_module modules/mod_jk-apache-2.2.4.so
Note: If you are planning to use apache with SSL, you must complete some additional configuration steps.
You must have openssl installed on your machine, version openssl-0.9.6g or higher. This can be downloaded from http://www.openssl.org/. If you have openssl installed on the machine, you can check the version:
openssl version
To create a test certificate, follow the instructions below (http://www.apache-ssl.org/#FAQ).
openssl req -new > new.cert.csr
openssl rsa -in privkey.pem -out new.cert.key
openssl x509 -in new.cert.csr -out new.cert.cert -req -signkey new.cert.key -days 365
After creating your test certificate, you must place the server.crt and server.key files where Apache can find them. This is configured in the folder /usr/local/extraview/httpd-2.2.21/conf/certs.
mkdir $BASE/httpd-2.2.21/conf/certs
mv new.cert.cert $BASE/httpd-2.2.21/conf/certs
mv new.cert.key $BASE/httpd-2.2.21/conf/certs
Edit the $BASE/httpd-2.2.21/conf/httpd.conf file to enable ssl as follows:
Find the line: # Secure (SSL/TLS) connections and uncomment the line below it:
include conf/extra/httpd-ssl.conf
Edit the $BASE/httpd-2.2.21/conf/extra/httpd-ssl.conf file as follows:
Find the line #SSLCertificateFile
Uncomment it and enter the correct path: /usr/local/extraview/httpd-2.2.21/conf/certs/new.cert.cert
Find the line #SSLCertificateKeyFile
Uncomment it and enter the correct path: /usr/local/extraview/httpd-2.2.21/conf/certs/new.cert.key
You can su to root and start/stop the apache ssl server using the following commands:
$BASE/httpd-2.2.21/bin/apachectl start
$BASE/httpd_2.2.21/bin/apachectl stop
If you enter the URL of server into a browser using the https protocol, for example https://server.domain.com, you should get the Apache test page.
Now edit the conf file to set up SSL.
vi $BASE/httpd-2.2.21/conf/extra/httpd-ssl.conf
Search for the beginning of the
DocumentRoot "/usr/local/extraview/httpd-2.2.21/htdocs"
ServerName www.example.com:443
ServerAdmin you@example.com
Comment these lines out.
At the bottom of the file, just above the line , paste in the following lines:
ServerName extraview.yourcompany.com
ServerAdmin you@example.com
DocumentRoot /usr/local/extraview/apache-tomcat-7.0.22/webapps/evj/
<Directory /usr/local/extraview/apache-tomcat-7.0.22/webapps/evj>
Options Indexes FollowSymLinks
Order allow,deny
Allow from all
</Directory>
<Location "/evj/WEB-INF/">
Order deny,allow
deny from all
</Location>
Alias /evj/ "/usr/local/extraview/apache-tomcat-7.0.22/webapps/evj/"
JkMount /evj/ExtraView/* tomcat1
JkMount /evj/ExtraView tomcat1
JkMount /evj/IsItEvj tomcat1
JkMount /evj/ConnectionPoolMon tomcat1
JkMount /evj/images/CompanyLogo.gif tomcat1
Edit these lines to reflect the correct ServerName, ServerAdmin and correct directory paths for DocumentRoot, Directory and Alias lines.
If you wish, you can edit the log paths:
ErrorLog "/usr/local/extraview/httpd-2.2.21/logs/error_log"
TransferLog "/usr/local/extraview/httpd-2.2.21/logs/access_log"
CustomLog "/usr/local/extraview/httpd-2.2.21/logs/ssl_request_log"
"%t %h %{SSL_PROTOCOL}x %{SSL_CIPHER}x \"%r\" %b"
Internet Explorer users of ExtraView will benefit from the following configuration. This greatly improves performance for these users. Find the section:
#BrowserMatch ".*MSIE.*"
# nokeepalive ssl-unclean-shutdown
# downgrade-1.0 force-response-1.0
and replace with the following:
BrowserMatch ".*MSIE [1-5].*"
nokeepalive ssl-unclean-shutdown
downgrade-1.0 force-response-1.0
BrowserMatch ".*MSIE [6-9].*"
ssl-unclean-shutdown
ExtraView ships with its JavaScript files in both a compressed and a non-compressed format. There may be a considerable speed advantage to using the compressed JavaScript files, especially if your users do not have access to a high bandwidth network. To enable the delivery of compressed JavaScript to your user's computers, set these directived in your httpd.conf file:
<FilesMatch ".js.gz$">
ForceType text/javascript
Header set Content-Encoding: gzip
</FilesMatch>
<FilesMatch ".js$">
RewriteEngine On
RewriteCond %{HTTP_USER_AGENT} !".*Safari.*"
RewriteCond %{HTTP:Accept-Encoding} gzip
RewriteCond %{REQUEST_FILENAME}.gz -f
RewriteRule (.*).js$ $1.js.gz [L]
ForceType text/javascript
</FilesMatch>
Now, find the following line in your httpd.conf file:
#LoadModule rewrite_module modules/mod_rewrite.so
Remove the comment character (#) at the beginning of the line.
Lastly, look for the line:
#LoadModule headers_module modules/mod_headers.so
and remove the comment character (#) from the beginning of the line.
The Apache server must be restarted after these changes.
The extraview.conf delivered with ExtraView contains a section that restricts access to the folders on the filesystem of the server that contain the ExtraView application.
<Location "/evj/WEB-INF/">
Order deny,allow
deny from all
</Location>
This default setting is predefined to work when configured to use a URL that looks like http://yourserver.yourdomain.com/evj/ExtraView to access ExtraView. If you have additional or different Apache configurations that perform redirection, URL rewriting or URL forwarding, it is important to test for a secure system to ensure that users do not have the ability to get a directory listing of the evj/WEB-INF folder or folders and the files they contain, as these files may contain sensitive information. Consult Apache documentation for additional details.